APIs power modern digital ecosystems. From mobile applications and SaaS platforms to cloud-native systems and AI services, APIs enable communication between applications, services, and users. However, as API usage grows, so do security threats. According to the OWASP API Security Top 10, API vulnerabilities are among the most critical risks in modern applications.
Securing APIs is not optional. It is essential for protecting sensitive data, maintaining user trust, and ensuring compliance with industry standards. In this comprehensive guide, we will explore API security fundamentals, common threats, authentication methods, best practices, and tools that help organizations safeguard their APIs effectively.
Table of Contents
Why API Security Is Critical
APIs often expose sensitive business logic and data. If improperly secured, attackers can exploit them to access confidential information, manipulate transactions, or disrupt services.
Common risks include:
- Data breaches
- Unauthorized access
- Injection attacks
- Broken authentication
- Excessive data exposure
The OWASP Foundation highlights broken object-level authorization and broken authentication as top API security vulnerabilities. Because APIs frequently connect multiple systems, a single weak endpoint can compromise an entire infrastructure.
Common API Security Threats
Understanding common threats is the first step toward securing APIs.
Broken Authentication and Authorization
Improper authentication mechanisms allow attackers to impersonate legitimate users. Weak token validation, missing access controls, or predictable API keys can lead to unauthorized access.
Injection Attacks
SQL injection, command injection, and other injection attacks occur when user input is not properly validated or sanitized. These attacks can compromise databases and backend systems.
Excessive Data Exposure
APIs sometimes expose more data than necessary. Without proper filtering and response control, sensitive fields such as passwords, tokens, or internal identifiers may leak.
Lack of Rate Limiting
Without rate limiting, APIs are vulnerable to brute-force attacks and denial-of-service attempts.
Insecure Direct Object References (IDOR)
Attackers manipulate object IDs in API requests to access unauthorized resources.
The detailed risk list is documented in the OWASP API Security Top 10.
Authentication and Authorization Best Practices
Authentication verifies identity, while authorization determines permissions. Both must be implemented correctly.
Use OAuth 2.0 and OpenID Connect
OAuth 2.0 is a widely adopted authorization framework that enables secure delegated access. It is commonly used with OpenID Connect for authentication. The official documentation from the OAuth 2.0 Framework explains secure implementation standards.
Implement JSON Web Tokens (JWT)
JWTs securely transmit information between parties. When properly signed and validated, JWTs ensure request authenticity. However, tokens must be:
- Signed with strong algorithms
- Expire within a reasonable timeframe
- Stored securely
The official resource at JWT.io provides implementation guidance.
Enforce Role-Based Access Control (RBAC)
RBAC ensures users can only access resources aligned with their roles. This prevents privilege escalation attacks.
Input Validation and Data Protection
Validate All Inputs
Never trust user input. Validate data types, length, and format before processing requests. Use server-side validation in addition to client-side validation.
Use HTTPS Everywhere
Transport Layer Security (TLS) encrypts data between clients and servers. All APIs must enforce HTTPS. The Cloudflare TLS Guide explains why encrypted connections are essential.
Encrypt Sensitive Data
Encrypt sensitive information at rest and in transit. Use strong encryption standards such as AES-256.
Limit Data Exposure
Return only necessary fields in API responses. Avoid exposing internal system details or debug information in production environments.
API Gateway and Rate Limiting
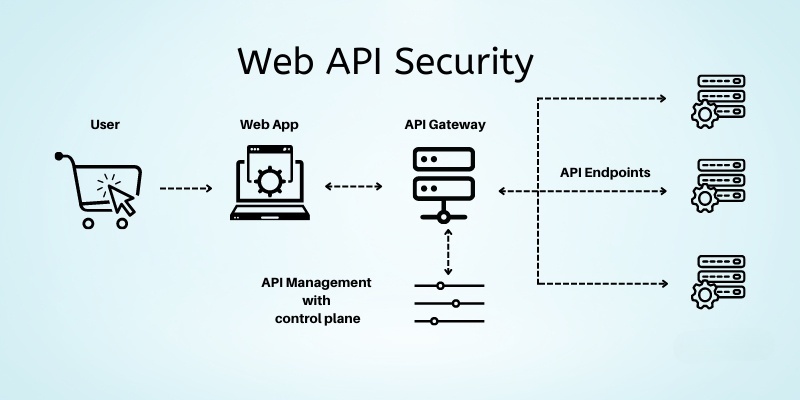
An API gateway acts as a security control layer between clients and backend services.
Use API Gateways
API gateways provide centralized authentication, logging, throttling, and monitoring. Solutions like Amazon API Gateway and Kong API Gateway offer built-in security features.
Implement Rate Limiting
Rate limiting prevents abuse by restricting the number of requests a client can make within a given timeframe. This mitigates brute-force and denial-of-service attacks.
Enable Web Application Firewalls (WAF)
A WAF filters and monitors HTTP traffic between clients and servers. It blocks malicious traffic patterns before they reach your API.
Logging, Monitoring, and Incident Response
Enable Comprehensive Logging
Log all API requests, authentication attempts, and failures. Ensure logs contain timestamps, user identifiers, and request metadata.
Monitor Anomalies
Use monitoring tools to detect unusual traffic spikes, repeated failed logins, or suspicious patterns. Platforms like Datadog and Prometheus help track API health and anomalies.
Prepare an Incident Response Plan
Even with strong security, breaches can occur. Prepare an incident response strategy that includes:
- Immediate isolation of compromised systems
- Revoking exposed tokens or credentials
- Notifying affected users
- Conducting post-incident analysis
DevSecOps: Integrating Security into the Development Lifecycle
Security should not be an afterthought. DevSecOps integrates security practices into CI/CD pipelines.
Use Automated Security Testing
Incorporate static application security testing (SAST) and dynamic application security testing (DAST) into your pipelines. Tools like SonarQube help identify vulnerabilities during development.
Conduct Regular Penetration Testing
Simulate real-world attacks to identify weaknesses before attackers do.
Keep Dependencies Updated
Outdated libraries often contain vulnerabilities. Regular updates and dependency scanning reduce risk exposure.
Conclusion
API security is a fundamental requirement for modern applications. As APIs connect systems, applications, and users, they become high-value targets for attackers. By implementing strong authentication methods, validating inputs, encrypting data, applying rate limits, and integrating security into the DevOps lifecycle, organizations can significantly reduce risks.
Also Check Infrastructure as Code – Powerful Infrastructure – 2026







1 thought on “How to Secure APIs – Protecting Modern Applications – 2026”